Not so long ago, I wrote a series of posts about Flowable:
- Getting started with Flowable
- Flowable's REST API - Part 1
- Flowable's REST API - Part 2
- Flowable's REST API - Part 3
- How To: Build Flowable
- How To: Flowable and LDAP
And recently, I wrote a series of posts about Keycloak:
In this post, I'll walk you through the steps I followed to get Keycloak to work with Flowable and OpenLDAP.
Getting Started
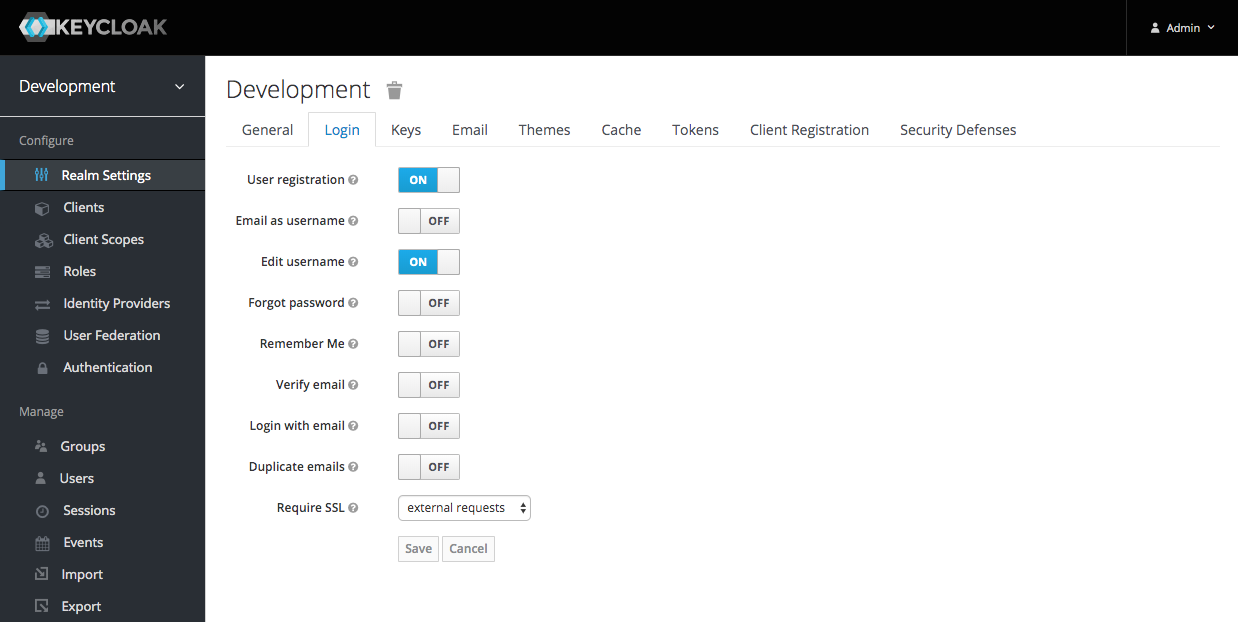
Flowable does not support email as username, so I had to update my realm's 'Login' settings:
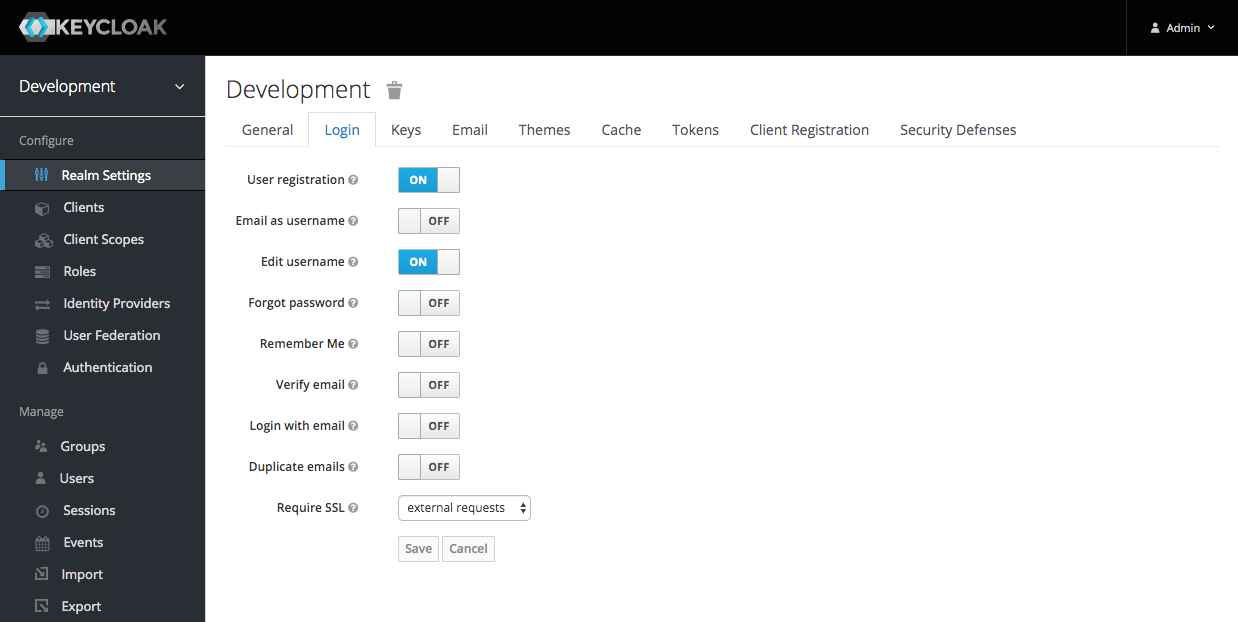
Check 'User registration' and 'Edit username'. Uncheck everything else and then click the 'Save' button.
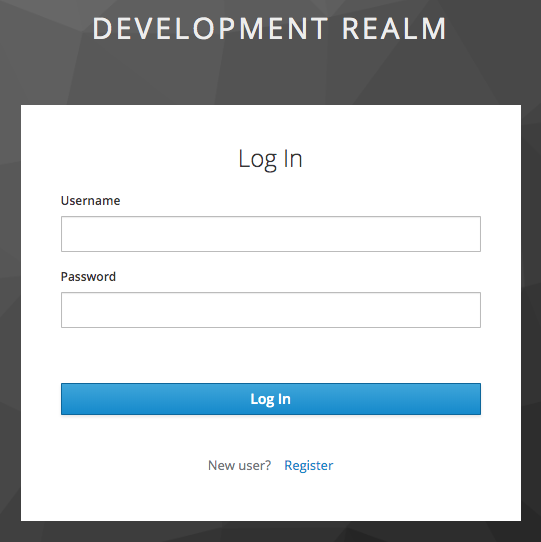
The Login (Username) page:
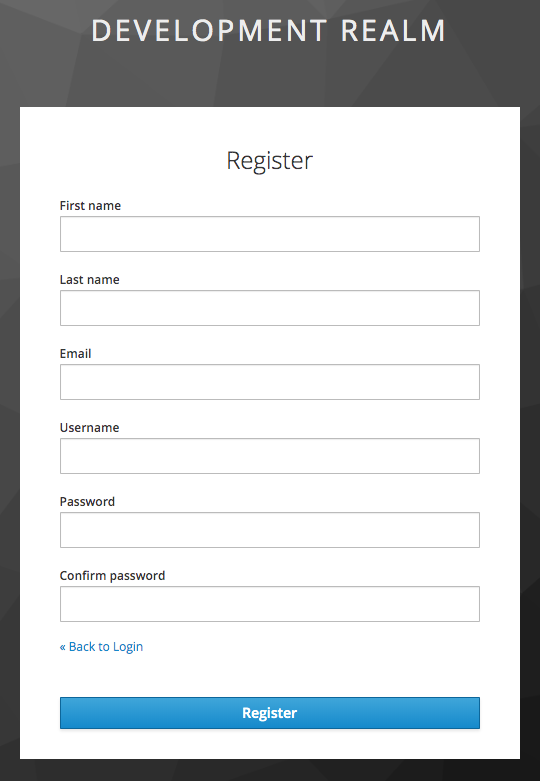
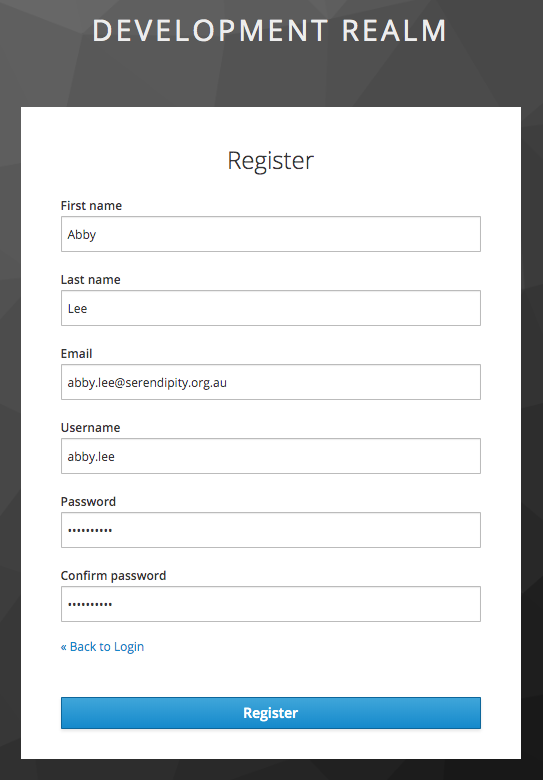
The Register (Username) page:
Flowable and OpenLDAP
Follow the steps in this post to configure Flowable to use OpenLDAP.
User Federation
To create a new User Federation click 'User Federation' in the sidemenu and then choose 'ldap' as the provider:
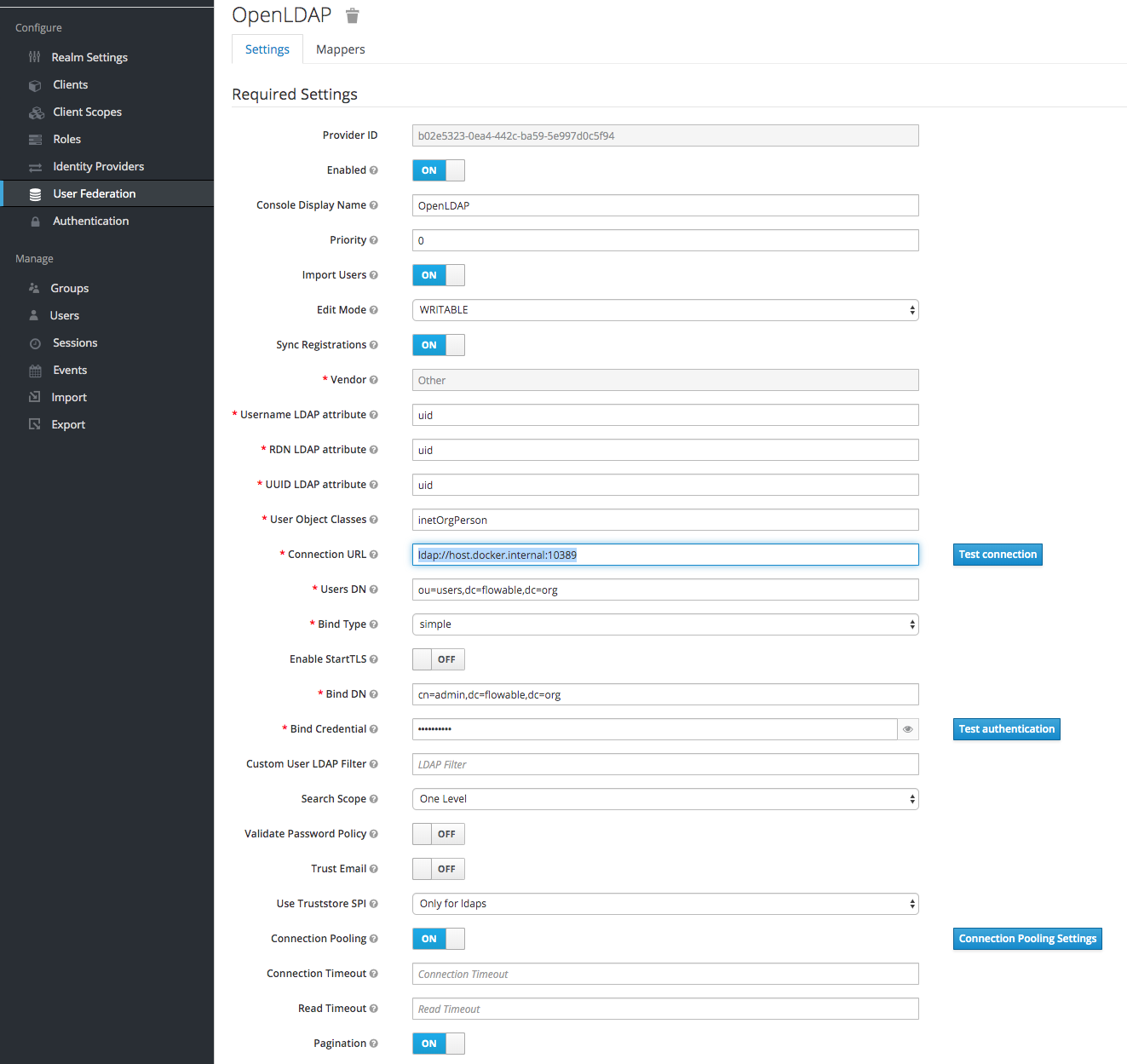
Check 'Enabled' and 'Import Users' then select 'Edit Mode: WRITABLE' and check 'Sync Registrations' so that user registrations will be created in OpenLDAP.
Select 'Vendor: Other' and enter 'uid' for the 'Username LDAP attribute', the 'RDN LDAP attribute' and the 'UID LDAP attribute'.
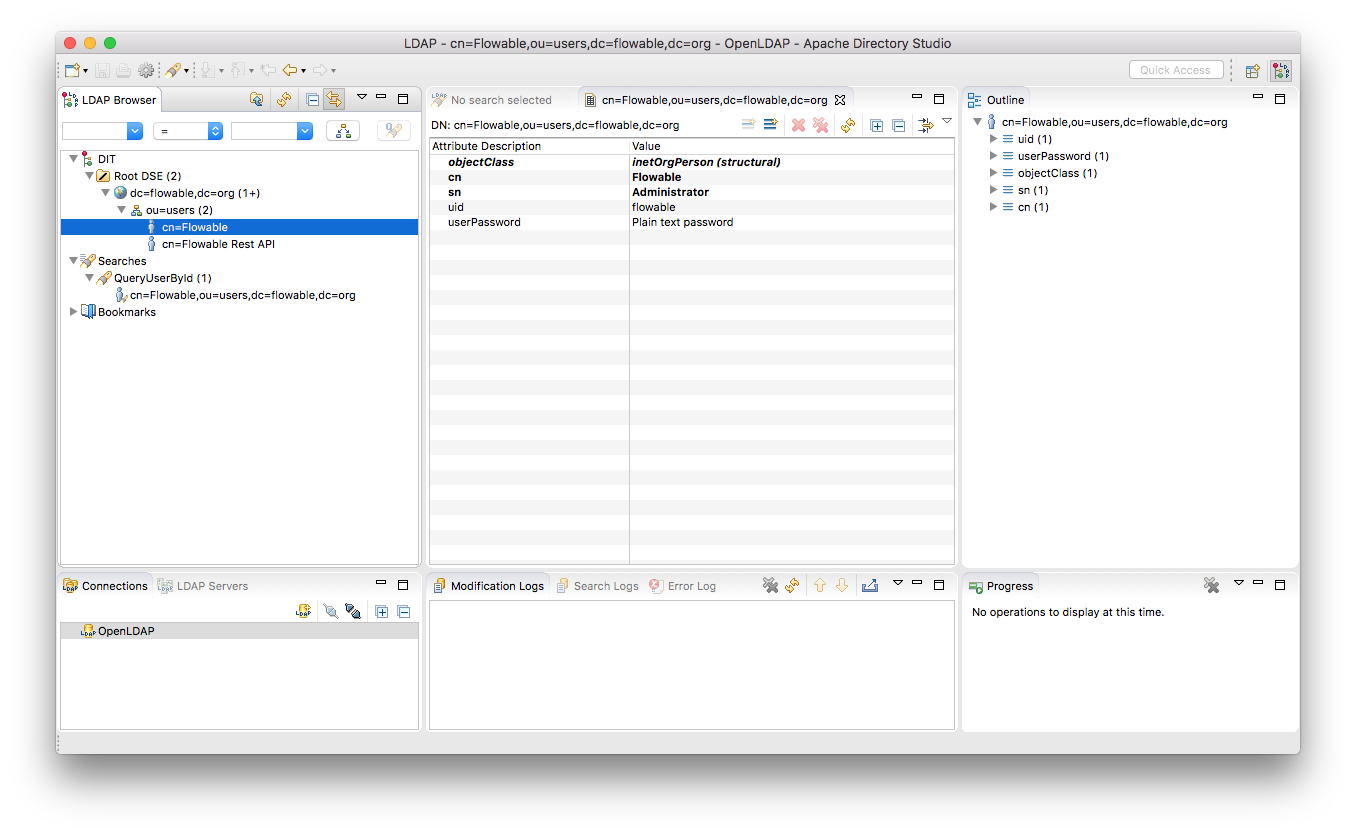
You can use an LDAP Browser to check your settings:
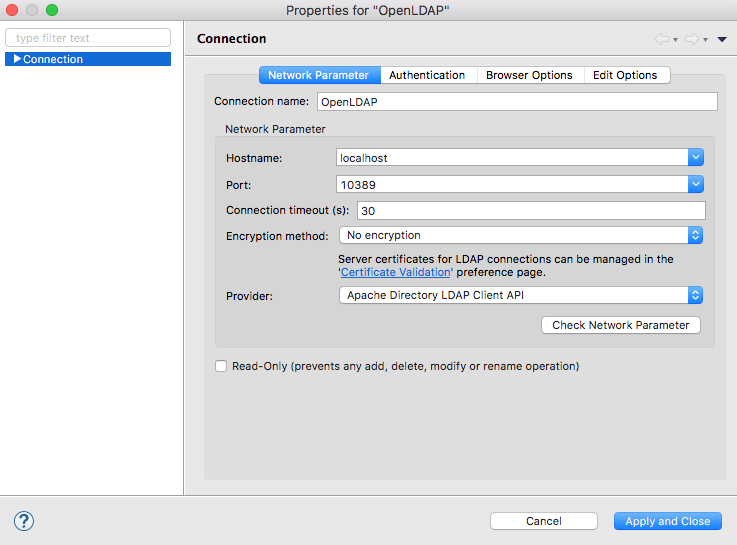
Network settings:
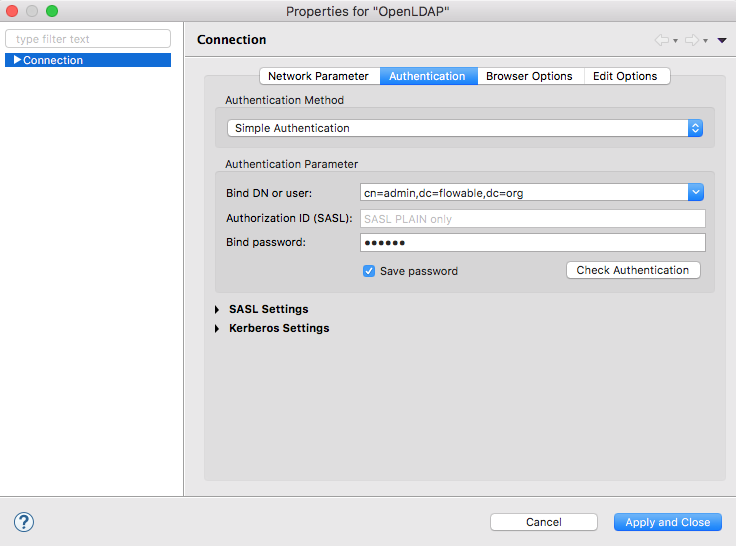
Authentication settings:
Note: I'm using Docker Desktop for Mac hence the need to use the special DNS name: host.docker.internal
User Registration
Now when a new user creates an account:
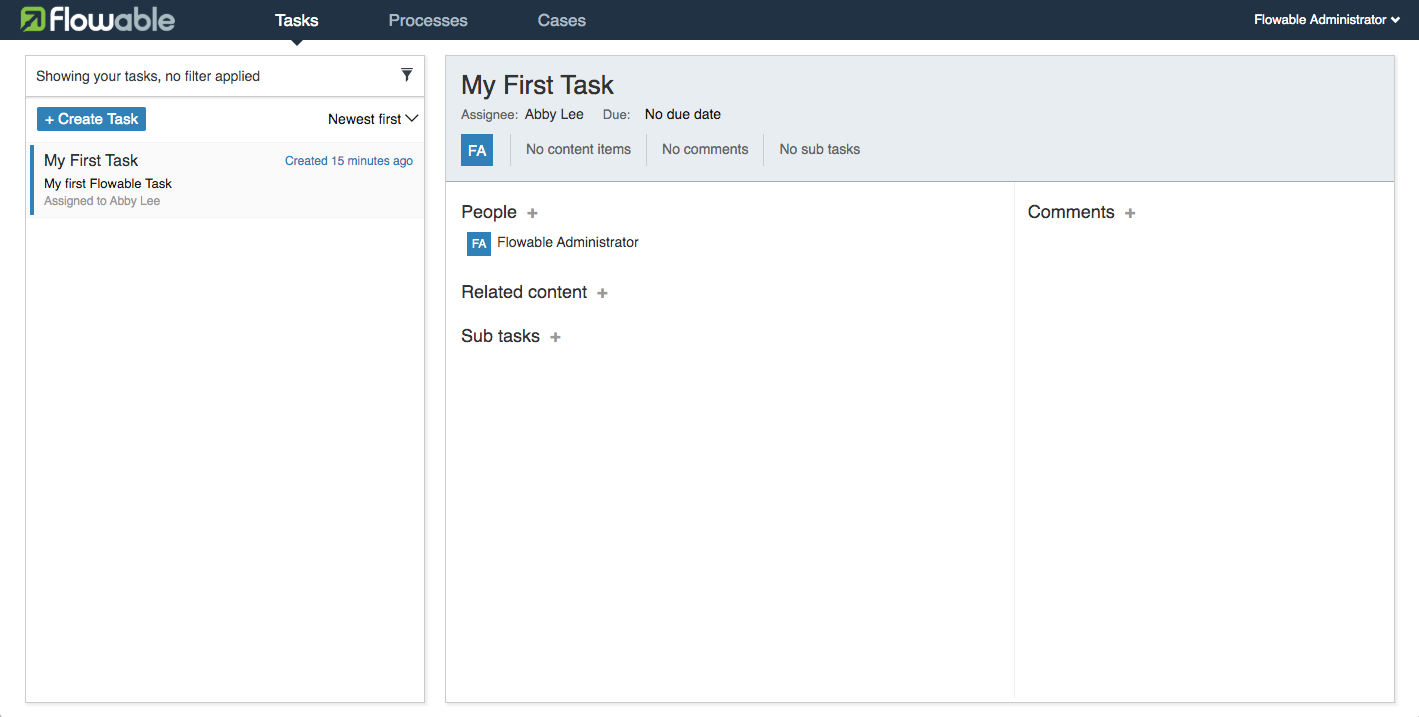
The new user is available in Flowable:
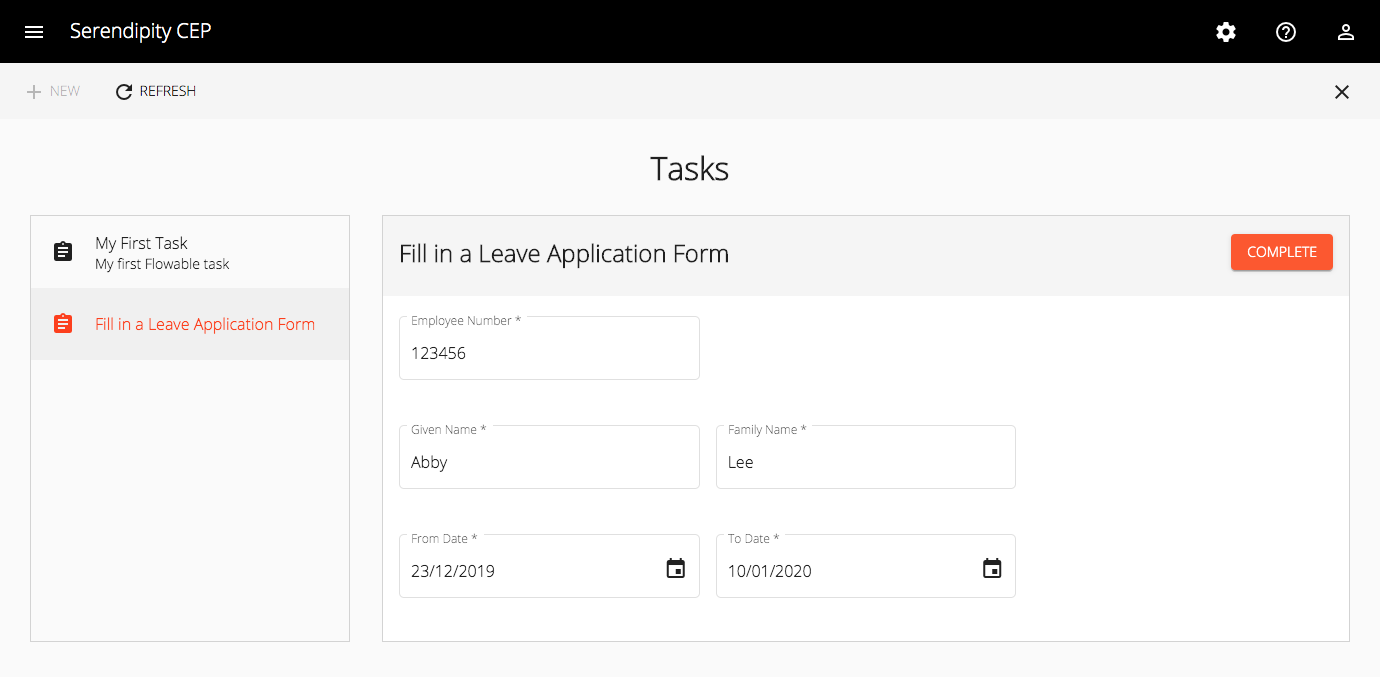
And in Serendipity:
Keycloak Issue
I raised the following Keycloak issue:
Afterword
Flowable's REST API supports HTTP Basic access authentication. I'm using Angular 8 and I had to update my proxy.conf.json as follows:
"/flowable-task": {
"target": "http://localhost:8080",
"secure": false,
"logLevel": "debug",
"headers": {
"Content-Type": "application/json",
"Authorization": "Basic Zmxvd2FibGUtcmVzdDp0ZXN0"
}
}
What's Next
In the next post, I'll walk you through the steps I followed to create a RESTful API (Resource Server) that embeds Flowable's BPMN engine, exposes the BPMN engine's RESTful API and leverages Spring Security’s support for OAuth 2.0 and Jason Web Tokens (JWTs).